Topic 3: Exam Pool C
The Chief Executive Officer (CEO) of an organization would like staff members to have the flexibility to work from home anytime during business hours, incident during a pandemic or crisis, However, the CEO is concerned that some staff members may take advantage of the of the flexibility and work from high-risk countries while on holidays work to a third-party organization in another country. The Chief information Officer (CIO) believes the company can implement some basic to mitigate the majority of the risk. Which of the following would be BEST to mitigate CEO’s concern? (Select TWO).
A.
Geolocation
B.
Time-of-day restrictions
C.
Certificates
D.
Tokens
E.
Geotagging
F.
Role-based access controls
Geolocation
Geotagging
A security analyst reviews the datacenter access logs for a fingerprint scanner and notices
an abundance of errors that correlate with users' reports of issues accessing the facility.
Which of the following MOST likely the cause of the cause of the access issues?
A.
False rejection
B.
Cross-over error rate
C.
Efficacy rale
D.
Attestation
Cross-over error rate
A cybersecurity administrator has a reduced team and needs to operate an on-premises network and security infrastructure efficiently. To help with the situation, the administrator decides to hire a service provider. Which of the following should the administrator use?
A.
SDP
B.
AAA
C.
IaaS
D.
MSSP
E.
Microservices
MSSP
A security analyst has been asked to investigate a situation after the SOC started to receive alerts from the SIEM. The analyst first looks at the domain controller and finds the following events: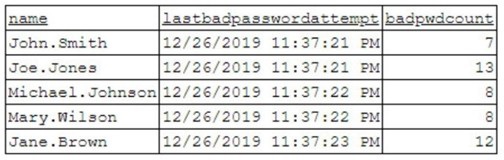
To better understand what is going on, the analyst runs a command and receives the
following output:
Based on the analyst’s findings, which of the following attacks is being executed?
A.
Credential harvesting
B.
Keylogger
C.
Brute-force
D.
Spraying
Spraying
A security engineer is reviewing log files after a third discovered usernames and passwords for the organization’s accounts. The engineer sees there was a change in the IP address for a vendor website one earlier. This change lasted eight hours. Which of the following attacks was MOST likely used?
A.
Man-in- the middle
B.
Spear-phishing
C.
Evil twin
D.
DNS poising
DNS poising
A technician needs to prevent data loss in a laboratory. The laboratory is not connected to
any external networks. Which of the following methods would BEST prevent the exfiltration of data? (Select TWO).
A.
VPN
B.
Drive encryption
C.
Network firewall
D.
File level encryption
E.
USB blocker
F.
MFA
Drive encryption
USB blocker
A security administrator suspects an employee has been emailing proprietary information to a competitor. Company policy requires the administrator to capture an exact copy of the employee’s hard disk. Which of the following should the administrator use?
A.
dd
B.
chmod
C.
dnsenum
D.
logger
dd
A user is concerned that a web application will not be able to handle unexpected or random
input without crashing. Which of the following BEST describes the type of testing the user
should perform?
A.
Code signing
B.
BFuzzing
C.
Manual code review
D.
Dynamic code analysis
Dynamic code analysis
A company processes highly sensitive data and senior management wants to protect the sensitive data by utilizing classification labels. Which of the following access control schemes would be BEST for the company to implement?
A.
Discretionary
B.
Rule-based
C.
Role-based
D.
Mandatory
Mandatory
The CSIRT is reviewing the lessons learned from a recent incident. A worm was able to spread unhindered throughout the network and infect a large number of computers and servers. Which of the following recommendations would be BEST to mitigate the impacts of a similar incident in the future?
A.
Install a NIDS device at the boundary.
B.
Segment the network with firewalls.
C.
Update all antivirus signatures daily.
D.
Implement application blacklisting.
Segment the network with firewalls.
Users at organization have been installing programs from the internet on their workstations
without first proper authorization. The organization maintains a portal from which users can
install standardized programs. However, some users have administrative access on their
workstations to enable legacy programs to function property. Which of the following should
the security administrator consider implementing to address this issue?
A.
Application code signing
B.
Application whitellsting
C.
Data loss prevention
D.
Web application firewalls
Application whitellsting
An organization has a growing workforce that is mostly driven by additions to the sales department. Each newly hired salesperson relies on a mobile device to conduct business. The Chief Information Officer (CIO) is wondering it the organization may need to scale down just as quickly as it scaled up. The ClO is also concerned about the organization's security and customer privacy. Which of the following would be BEST to address the ClO’s concerns?
A.
Disallow new hires from using mobile devices for six months
B.
Select four devices for the sales department to use in a CYOD model
C.
Implement BYOD for the sates department while leveraging the MDM
D.
Deploy mobile devices using the COPE methodology
Implement BYOD for the sates department while leveraging the MDM
| Page 5 out of 74 Pages |
| Previous |