Which of the log storage method arranges event logs in the form of a circular buffer?
A.
FIFO
B.
LIFO
C.
non-wrapping
D.
wrapping
FIFO
According to the Risk Matrix table, what will be the risk level when the probability of an attack is very high, and the impact of that attack is major?
NOTE: It is mandatory to answer the question before proceeding to the next one.
A.
High
B.
Extreme
C.
Low
D.
Medium
High
Reference: https://onlinelibrary.wiley.com/page/journal/15396924/homepage/
special_issue
simple_characterisations_and_communication_of_risks.htm
Rinni, SOC analyst, while monitoring IDS logs detected events shown in the figure below.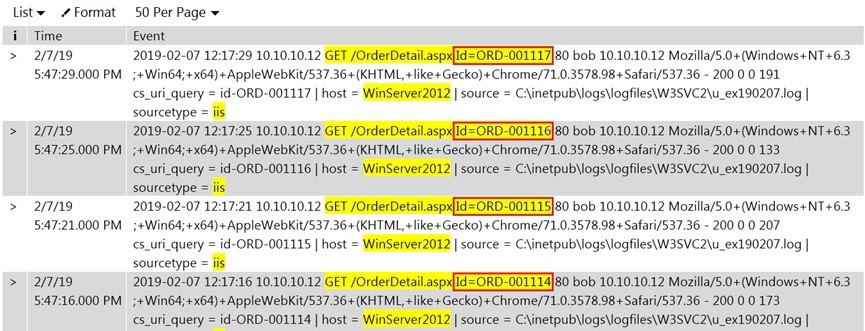
What does this event log indicate?
A.
Directory Traversal Attack
B.
XSS Attack
C.
SQL Injection Attack
D.
Parameter Tampering Attack
Parameter Tampering Attack
Reference: https://infosecwriteups.com/what-is-parameter-tampering-5b1beb12c5ba
The threat intelligence, which will help you, understand adversary intent and make
informed decision to ensure appropriate security in alignment with risk.
What kind of threat intelligence described above?
A.
Tactical Threat Intelligence
B.
Strategic Threat Intelligence
C.
Functional Threat Intelligence
D.
Operational Threat Intelligence
Strategic Threat Intelligence
Reference: https://www.blueliv.com/cyber-security-and-cyber-threat-intelligence-blogblueliv/
threat- intelligence/what-is-threat-intelligence/
An attacker exploits the logic validation mechanisms of an e-commerce website. He
successfully purchases a product worth $100 for $10 by modifying the URL exchanged
between the client and the server.
Original URL: http://www.buyonline.com/product.aspx?profile=12&debit=100 Modified URL:
http://www.buyonline.com/product.aspx?profile=12&debit=10
Identify the attack depicted in the above scenario.
A.
Denial-of-Service Attack
B.
SQL Injection Attack
C.
Parameter Tampering Attack
D.
Session Fixation Attack
Session Fixation Attack
An organization wants to implement a SIEM deployment architecture. However, they have the capability to do only log collection and the rest of the SIEM functions must be managed
by an MSSP. Which SIEM deployment architecture will the organization adopt?
A.
Cloud, MSSP Managed
B.
Self-hosted, Jointly Managed
C.
Self-hosted, MSSP Managed
D.
Self-hosted, Self-Managed
Self-hosted, MSSP Managed
Which of the following process refers to the discarding of the packets at the routing level without informing the source that the data did not reach its intended recipient?
A.
Load Balancing
B.
Rate Limiting
C.
Black Hole Filtering
D.
Drop Requests
Black Hole Filtering
Reference:
https://en.wikipedia.org/wiki/Black_hole_(networking)#:~:text=In-networking%2C-bl
ack% 20holes-refer,not-reach-its-intended-recipient.
Which of the following steps of incident handling and response process focus on limiting the scope and extent of an incident?
A.
Containment
B.
Data Collection
C.
Eradication
D.
Identification
Containment
Which of the following tool is used to recover from web application incident?
A.
CrowdStrike FalconTM Orchestrator
B.
Symantec Secure Web Gateway
C.
Smoothwall SWG
D.
Proxy Workbench
Symantec Secure Web Gateway
Which of the following fields in Windows logs defines the type of event occurred, such as Correlation Hint, Response Time, SQM, WDI Context, and so on?
A.
Keywords
B.
Task Category
C.
Level
D.
Source
Keywords
Which of the following command is used to view iptables logs on Ubuntu and Debian distributions?
A.
$ tailf /var/log/sys/kern.log
B.
$ tailf /var/log/kern.log
C.
# tailf /var/log/messages
D.
# tailf /var/log/sys/messages
$ tailf /var/log/kern.log
Reference: https://tecadmin.net/enable-logging-in-iptables-on-linux/
What does HTTPS Status code 403 represents?
A.
Unauthorized Error
B.
Not Found Error
C.
Internal Server Error
D.
Forbidden Error
Forbidden Error
| Page 3 out of 9 Pages |
| Previous |