Topic 5: Exam Pool E
Maintaining the chain of custody is an important part of the incident response process. Which of the following reasons explains why this is important?
A. To maintain an information security policy
B. To properly identify the issue
C. To control evidence and maintain integrity
D. To gather as much information as possible
Explanation: Maintaining the chain of custody is important to control evidence and maintain integrity. The chain of custody is a process that documents who handled, accessed, or modified a piece of evidence, when, where, how, and why. The chain of custody ensures that the evidence is preserved, protected, and authenticated throughout the incident response process. Maintaining the chain of custody can help prevent tampering, alteration, or loss of evidence, as well as establish its reliability and validity in legal proceedings. Maintaining an information security policy, properly identifying the issue, and gathering as much information as possible are not reasons why maintaining the chain of custody is important. Maintaining an information security policy is a general practice that defines the rules and guidelines for securing an organization’s information assets and resources. Properly identifying the issue is a step in the incident response process that involves analyzing and classifying the incident based on its severity, impact, and scope. Gathering as much information as possible is a step in the incident response process that involves collecting and documenting relevant data and evidence from various sources, such as logs, alerts, or witnesses.
A management team at a small office wants to block access to inappropriate websites and create a log of these access attempts. Which of the following is a way to meet these requirements?
A. Content filter
B. Screened subnet
C. Port forwarding
D. Access control list
An administrator has submitted a change request for an upcoming server deployment. Which of the following must be completed before the change can be approved?
A. Risk analysis
B. Sandbox testing
C. End user acceptance
D. Lessons learned
Explanation: Risk analysis is the process of identifying and evaluating the potential threats and impacts of a change on the system, network, or service. It is an essential step before approving a change request, as it helps to determine the level of risk, the mitigation strategies, and the contingency plans. Risk analysis also helps to prioritize the change requests based on their urgency and importance12.
A user's antivirus software reports an infection that it is unable to remove. Which of the following is the most appropriate way to remediate the issue?
A. Disable System Restore.
B. Utilize a Linux live disc.
C. Quarantine the infected system.
D. Update the anti-malware.
Explanation:
Quarantining the infected system is the most appropriate way to remediate the issue of an infection that the antivirus software cannot remove. Quarantining means isolating the system from the network and other devices to prevent the infection from spreading or causing further damage. Quarantining also allows the technician to perform further analysis and removal of the infection without risking the security of other systems or data.
Some of the steps involved in quarantining an infected system are:
Disconnect the system from the internet and any local network connections, such as Wi-Fi, Ethernet, Bluetooth, or USB.
Disable any file-sharing or remote access services on the system, such as Windows File Sharing, Remote Desktop, or TeamViewer.
Use a separate device to download and update the antivirus software and any other tools that may be needed to remove the infection, such as malware scanners, rootkit removers, or bootable rescue disks.
Transfer the updated antivirus software and tools to the infected system using a removable media, such as a CD, DVD, or USB flash drive. Scan the removable media for any infections before and after using it on the infected system.
Run the antivirus software and tools on the infected system and follow the instructions to delete or quarantine the infection. If the infection is persistent or complex, it may require booting the system from a rescue disk or using a Linux live disc to access and clean the system files.
After the infection is removed, restore the system to a previous clean state using System Restore, backup, or recovery partition. Scan the system again to ensure that it is clean and secure. Reconnect the system to the network and update the system and the antivirus software.
A user reports seeing random, seemingly non-malicious advertisement notifications in the Windows 10 Action Center. The notifications indicate the advertisements are coming from a web browser. Which of the following is the best solution for a technician to implement?
A. Disable the browser from sending notifications to the Action Center.
B. Run a full antivirus scan on the computer.
C. Disable all Action Center notifications.
D. Move specific site notifications from Allowed to Block.
When trying to access a secure internal network, the user receives an error messaging stating, "There is a problem with this website's security certificate." The user reboots the desktop and tries to access the website again, but the issue persists. Which of the following should the user do to prevent this error from reoccurring?
A. Reimage the system and install SSL.
B. Install Trusted Root Certificate.
C. Select View Certificates and then Install Certificate.
D. Continue to access the website.
Explanation: The error message indicates that the website’s security certificate is not trusted by the user’s device, which may prevent the user from accessing the secure internal network. To resolve this issue, the user can view the certificate details and install it on the device, which will add it to the trusted root certificate store. Reimaging the system and installing SSL, installing Trusted Root Certificate, or continuing to access the website are not recommended solutions, as they may compromise the security of the device or the network.
A user clicks a link in an email. A warning message in the user's browser states the site's certificate cannot be verified. Which of the following is the most appropriate action for a technician to take?
A. Click proceed.
B. Report the employee to the human resources department for violating company policy.
C. Restore the computer from the last known backup.
D. Close the browser window and report the email to IT security.
Which of the following statements describes the purpose of scripting languages? To access the hardware of the computer it is running on
A. To automate tasks and reduce the amount of manual labor
B. To abstract the complexity of the computer system
C. To compile the program into an executable file
Explanation: Scripting languages are used to write small to medium-sized programs that perform specific tasks. Some common uses of scripting languages are: automating repetitive processes, web development, system administration, data processing, multimedia and games, report generation, document and text processing, writing plugins and extensions for existing programs and applications1.
A hotel's Wi-Fi was used to steal information on a corporate laptop. A technician notes the following security log:
SRC: 192.168.1.1/secrets.zip Protocol SMB >> DST: 192.168.1.50/capture The technician analyses the following Windows firewall information:
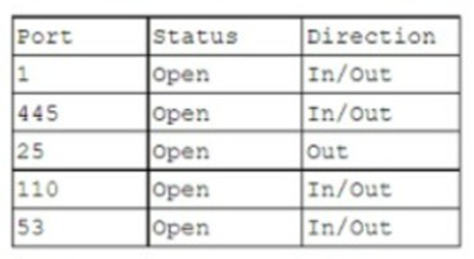
Which of the following protocols most likely allowed the data theft to occur?
A. 1
B. 53
C. 110
D. 445
Explanation: The protocol that most likely allowed the data theft to occur is SMB over TCP port 445. SMB is a network file sharing protocol that enables access to files, printers, and other resources on a network. Port 445 is used by SMB to communicate directly over TCP without the need for NetBIOS, which is an older and less secure protocol. The security log shows that the source IP address 192.168.1.1 sent a file named secrets.zip using SMB protocol to the destination IP address 192.168.1.50, which captured the file. The Windows firewall information shows that port 445 is enabled for inbound and outbound traffic, which means that it is not blocked by the firewall. Therefore, port 445 is the most likely port that was exploited by the attacker to steal the data from the corporate laptop.
An employee has repeatedly contacted a technician about malware infecting a work computer. The technician has removed the malware several times, but the user's PC keeps getting infected. Which of the following should the technician do to reduce the risk of future infections?
A. Configure the firewall.
B. Restore the system from backups.
C. Educate the end user
D. Update the antivirus program.
Explanation: Malware is software that infects computer systems to damage, disable or exploit the computer or network for various malicious purposes5. Malware is typically distributed via email attachments, fake internet ads, infected applications or websites, and often relies on user interaction to execute6. Therefore, one of the most effective ways to prevent malware infections is to educate the end user about the common signs and sources of malware, and how to avoid them7. Configuring the firewall, restoring the system from backups, and updating the antivirus program are also important security measures, but they do not address the root cause of the user’s repeated infections, which is likely due to a lack of awareness or caution.
A customer calls desktop support and begins yelling at a technician. The customer claims to have submitted a support ticket two hours ago and complains that the issue still has not been resolved. Which of the following describes how the technician should respond? Place the customer on hold until the customer calms down.
A. Disconnect the call to avoid a confrontation.
B. Wait until the customer is done speaking and offer assistance.
C. Escalate the issue to a supervisor.
A technician is building a new desktop machine for a user who will be using the workstation to render 3-D promotional movies. Which of the following is the most important component?
A. Dedicated GPU
B. DDR5 SODIMM
C. NVMe disk
D. 64-bit CPU
| Page 2 out of 62 Pages |
| Previous |